
Posted on Thursday, Sep 28th, 2023
Navigating the Storm: Recovering from a Cybersecurity Incident
Have you formulated your cyber security incident response plan?
If not yet, then let’s make it quick. Because the probability of your company becoming the next target of a cyberattack is surprisingly significant. Considering some recent surveys, with the widespread adoption of remote work policies, cybercrimes have surged by a staggering 600%.
The impact of cyberattacks can vary widely. Some can swiftly incapacitate your networks, while others may remain hidden for extended periods, going undetected for weeks or even months. However, what remains constant is their capacity to inflict substantial harm on your company, both in terms of financial repercussions and damage to your reputation. In some cases, recovery from cyber-attack may prove to be an immensely challenging endeavour.
So, it’s important to recognize that cybercriminals can exploit even the smallest cybersecurity gap in your cybersecurity infrastructure or a simple click on a misleading link to infiltrate your company's computer systems, potentially compromising sensitive digital information.
It is imperative not only to engage the services of a reliable cyber security service provider but also to comprehend the potential ramifications that the absence of such expertise can entail in the event of a disaster.
What is a Cyber Security Incident Response Plan
A Cyber Security Incident Response Plan (CSIRP) is a comprehensive strategy and set of documented procedures designed to guide an organization's response to cybersecurity incidents. It outlines the steps to be taken when a security breach or incident occurs, with the aim of minimizing damage, reducing recovery time, and ensuring effective communication and coordination among relevant stakeholders. A CSIRP typically includes the following key components:1. Purpose and Scope
Define the objectives and scope of the incident response plan, including the types of incidents it covers.2. Roles and Responsibilities
Specify the roles and responsibilities of individuals and teams involved in the incident response process. This includes incident response team members, IT staff, legal, communications, and management.3. Incident Classification and Severity Levels
Define criteria for classifying incidents based on their severity and potential impact on the organization.4. Incident Detection and Reporting
Describe how incidents are detected and reported, including the use of security monitoring tools and the process for employees to report suspicious activities.5. Incident Assessment and Triage
Outline procedures for assessing the nature and scope of the incident, including gathering relevant information and conducting initial triage.6. Incident Containment and Eradication
Detail steps for isolating affected systems or networks, blocking malicious activity, and eliminating the root cause of the incident.7. Communication and Notification
Specify who needs to be informed about the incident, both internally and externally, and provide guidelines for communicating with stakeholders, law enforcement, and regulatory authorities.8. Legal and Regulatory Compliance
Address legal and compliance considerations, including data breach notification requirements and preservation of evidence for potential legal actions.9. Evidence Collection and Preservation
Explain how digital evidence is collected, preserved, and documented to support investigations and potential legal proceedings.10. Incident Recovery and System Restoration
Detail the steps to restore affected systems, verify their integrity, and monitor for any signs of re-infection.11. Lessons Learned and Post-Incident Analysis
Describe the process for conducting post-incident reviews to identify root causes, vulnerabilities, and lessons learned. This should lead to improvements in security measures.12. Training and Awareness
Outline ongoing training and awareness programs to ensure that staff members are informed about the CSIRP and know how to respond to incidents.13. Testing and Exercising
Specify how the incident response plan is regularly tested through tabletop exercises, simulations, or drills to ensure its effectiveness.14. Documentation and Record Keeping
Emphasize the importance of maintaining detailed records of incident response activities for legal, regulatory, and auditing purposes.15. Plan Maintenance and Review
Highlight the need for periodic reviews and updates to the CSIRP to keep it aligned with evolving threats and organizational changes.Cyber Security Incident Response Process
Implementing a well-defined process significantly conserves valuable time and effort. Below are some strategic approaches towards cyber-attack recovery:1. Immediate Response and Assessment
In the immediate aftermath of an incident, it's crucial to assemble a response team that includes IT professionals, legal advisors, and communication experts. This team should swiftly assess the extent of the breach, identify compromised systems, and mitigate ongoing threats.2. Communication Strategy
Transparency is key. Develop a comprehensive communication plan that addresses both internal and external stakeholders. Notify affected parties promptly, providing accurate information on the incident, its impact, and the steps being taken to rectify the situation. Maintain clear and consistent messaging to prevent misinformation.3. Legal and Regulatory Compliance
Ensure that your response complies with all relevant laws and regulations. This may involve reporting the incident to authorities or notifying affected individuals in accordance with data breach notification requirements.4. Recovery and Restoration
Collaborate closely with IT teams to restore affected systems and data. Implement enhanced security measures and conduct a thorough forensic analysis to identify the root cause of the breach and prevent a recurrence.5. Rebuilding Trust
Rebuilding trust takes time. Demonstrate your commitment to security by investing in robust cybersecurity measures and best practices. Regularly update clients and stakeholders on progress made in strengthening security.6. Customer Support
Provide dedicated support to affected clients. Offering solutions and assistance can go a long way in retaining their trust and loyalty. Personalize your interactions to make clients feel valued and supported during the recovery process.7. Educational Initiatives
Launch educational campaigns for both employees and clients to raise awareness about cybersecurity threats and best practices. Knowledge is a powerful defense against future incidents.8. Continuous Monitoring and Improvement
Implement a continuous monitoring system to detect and respond to potential threats in real-time. Regularly review and update your cybersecurity policies and cyber security incident response plans based on lessons learned.9. Public Relations
Work closely with PR professionals to manage media coverage and public perception. Craft a narrative that emphasizes your commitment to security and recovery efforts, turning the incident into an opportunity to showcase resilience and growth.10. Third-Party Assessment
Consider engaging third-party cybersecurity experts to conduct an independent assessment of your security posture. This can provide assurance to stakeholders that you are taking proactive steps to prevent future incidents.The Risks of Not Having a Disaster Recovery Plan
The risks of not having a disaster recovery plan in place for your business cannot be overstated. Without a well-thought-out and tested plan, your organization is vulnerable to a range of potential negative consequences, including:1. Data Loss
One of the most significant risks is the loss of critical data. Whether due to a natural disaster, cyberattack, hardware failure, or human error, data can be permanently lost without a proper backup and recovery strategy. This loss can result in business disruptions, financial losses, and legal issues.2. Downtime and Productivity Loss
When disaster strikes, and your systems are not backed up or recoverable, your business operations may come to a halt. Extended downtime can result in lost revenue, missed opportunities, and damage to your reputation. Employees may be unable to work, leading to productivity losses.3. Financial Impact
The financial implications of not having a disaster recovery plan can be severe. In addition to the cost of data recovery (if possible), you may face expenses related to repairing or replacing damaged equipment, legal fees, regulatory fines, and potential lawsuits from customers or partners affected by data breaches.4. Reputation Damage
Customers and partners rely on businesses to protect their data and ensure the continuity of services. If a disaster disrupts your operations and customer data is compromised, your reputation can suffer irreparable harm. Rebuilding trust can be a long and challenging process.5. Regulatory Non-Compliance
Many industries have regulations that require organizations to have a cyber security incident response plan in place. Failure to comply with these regulations can lead to fines and legal consequences. It can also damage relationships with clients who expect their data to be handled in a compliant manner.6. Competitive Disadvantage
Businesses that lack a plan for recovery from cyber-attack may struggle to compete with competitors who can guarantee the availability and security of their services. Clients and partners are more likely to choose companies that demonstrate a commitment to data protection and business continuity.7. Supply Chain Disruptions
Your business may rely on a network of suppliers and partners. If a disaster affects one of these critical links, it can disrupt your supply chain, impacting your ability to deliver products or services on time and meet customer demands.8. Loss of Intellectual Property
For businesses that rely on proprietary technology or intellectual property, not having a disaster recovery plan exposes them to the risk of losing valuable assets. Competitors or malicious actors may take advantage of this vulnerability.9. Employee Morale and Turnover
When employees witness a lack of preparedness in the face of a disaster, it can negatively impact their morale. High-stress situations and extended downtime can lead to increased turnover as employees seek more stable work environments.10. Inability to Scale
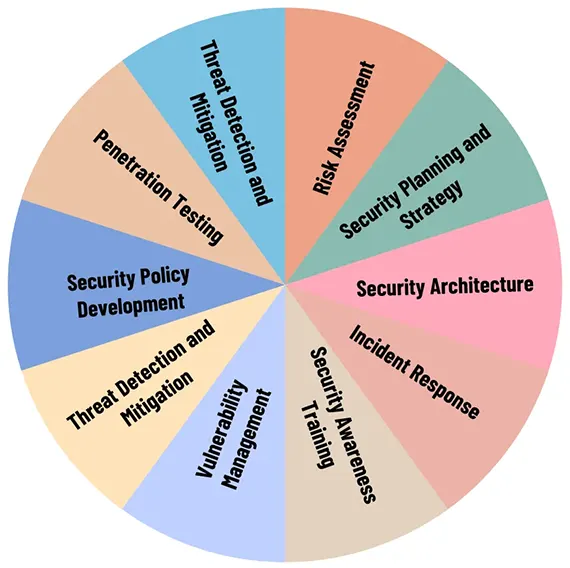
Without a plan for recovery from cyber-attack, your business may find it challenging to scale up or expand. Investors and potential partners may be hesitant to get involved with a company that does not prioritize risk management.Responsibilities of a Cyber Security Service Provider
Conclusion
Recovery from cyber-attack can be just as formidable as the attack itself. At Blue Summit, our dedicated team tirelessly initiates the recovery process, diligently restoring compromised systems, and fortifying your cybersecurity defenses both during and after the incident. We prioritize minimizing the disruption for you throughout the recovery phase.Our well-crafted cyber security incident response plan is a critical component of an organization's overall cybersecurity strategy. It helps you minimize the impact of cyber incidents, reduces recovery time, and enhances the organization's resilience in the face of evolving cyber threats. As a reputable and certified cyber security service provider, opt for Blue Summit today to ensure your ongoing security and peace of mind.
Blue Summit has collaborated with OdiTek Solutions, a frontline custom software development company. It is trusted for its high service quality and delivery consistency. Visit our partner's page today and get your business streamlined.
REFER TO OTHER RELEVANT CONTENTS

Navigating the Storm: Recovering from a Cybersecurity Incident
Have you formulated your cyber security incident response plan? If not yet, then let’s make it quick. Because the probability of your company becoming the next target of a cyberattack is surprisingly significant. Considering some recent surveys, with the widespread adoption of remote work policies,...
read more
Consulting
At Blue Summit, our goal is solely to help our clients leverage their technology investments to improve business performance. We deliver tailored IT consultancy solutions and business IT support to organizations of any size. With Blue Summit as your partner, we can help lead your organization forward with highly effective IT strategies and implement innovative business solutions.
read more







